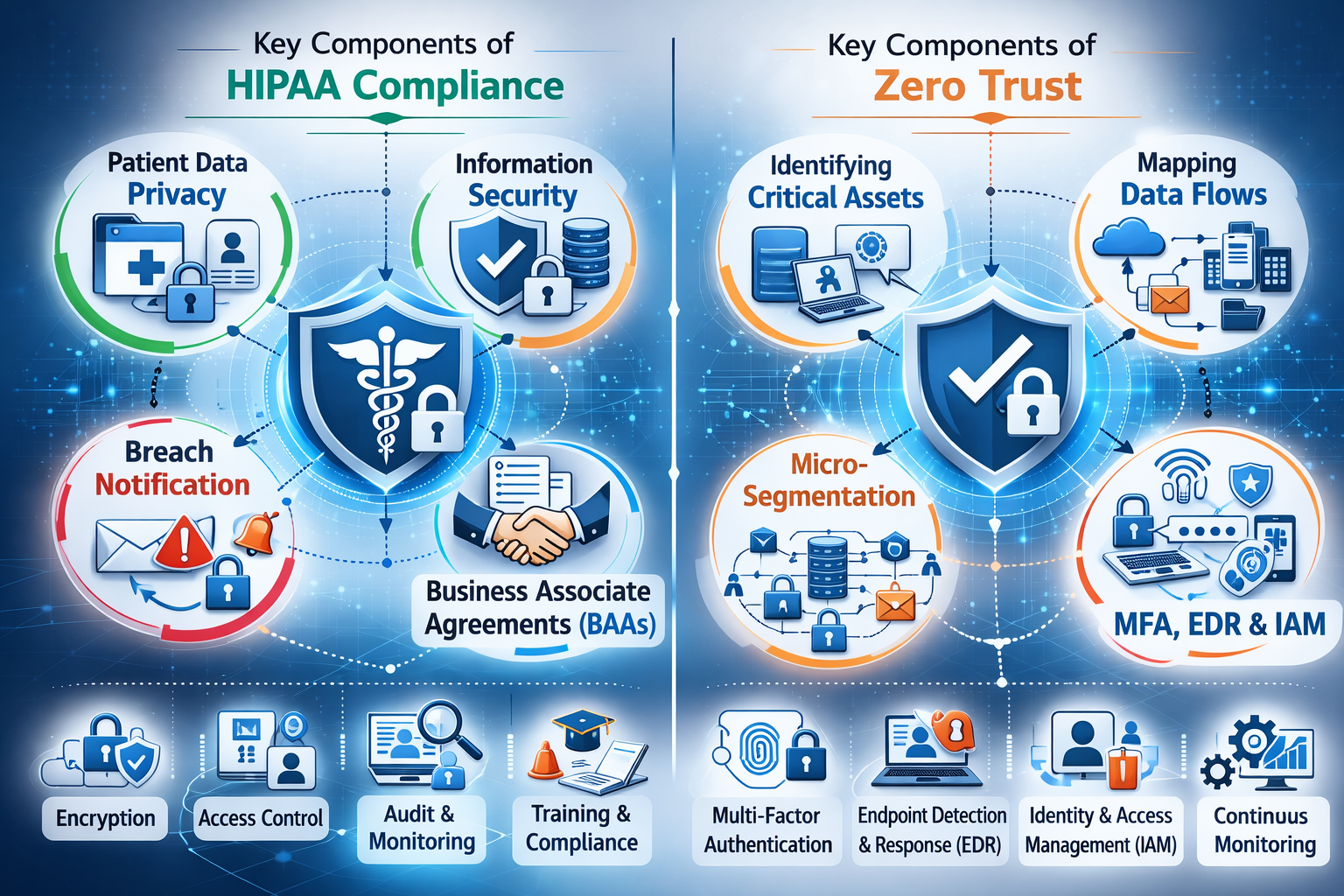
Healthcare cybersecurity protects patient privacy, clinical continuity, and legal accountability — using HIPAA-aligned controls and a Zero Trust security model.
Hospitals, clinics and health networks process highly sensitive patient records (PHI/ePHI), diagnostic data, insurance interactions, and transactional systems. As healthcare becomes digital, cyber incidents can cause service disruption, information leakage, fraud exposure, reputational damage and potential lawsuits.
Healthcare has one of the highest risk profiles because systems must remain available, accurate, and confidential. A cyber incident in healthcare is not just an IT problem — it can disrupt patient care, delay treatment, expose records, and create significant legal and reputational consequences.
Zero Trust protects healthcare environments where users, departments, devices and partners constantly interact. Instead of assuming trust inside the network, Zero Trust continuously verifies identity, device health, access intent and policy compliance.
Quest secures healthcare environments by combining HIPAA-aligned controls with a Zero Trust approach�protecting patient data (PHI/ePHI), hospital transactional systems, and clinical uptime across on-prem, cloud and remote access.
Deliverable: Risk-ranked report + remediation roadmap ready for RFQ scope.
Healthcare is a core sector for Quest. We deliver structured assessments, practical remediation roadmaps, and implementation support to secure patient data and hospital operations in Kenya and East Africa.