Why better detection and response has become a business priority
Cyber threats are no longer isolated endpoint incidents. They move across users, endpoints, network paths, email, cloud services, and business applications, often remaining undetected until damage is already underway. For organizations in Kenya and East Africa, the challenge is no longer only prevention. It is whether the business has the right visibility and response capability to detect, investigate, and contain threats before operational, financial, or regulatory impact occurs.
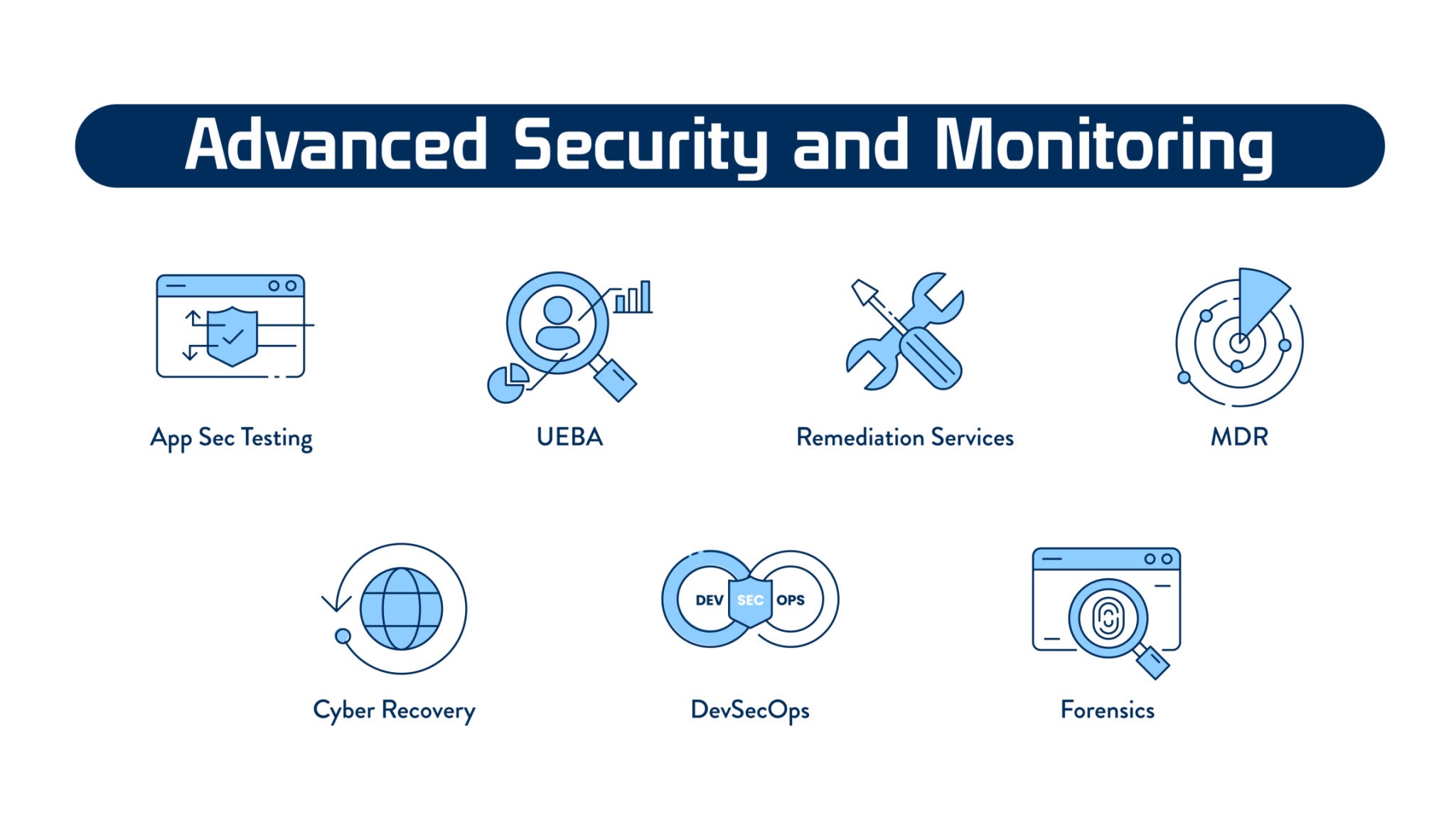
This is why EDR, XDR, and MDR have become central to modern security strategy. They address different levels of detection and response maturity, and the right decision depends on the complexity of the environment, the internal team’s capability, and the organization’s operational risk profile.
What is EDR?
Endpoint Detection and Response focuses on endpoint activity across laptops, desktops, servers, and workstations. It captures behavior on devices, detects suspicious activity, and supports automated or guided response actions such as isolating a compromised machine. EDR is especially valuable where the immediate need is stronger endpoint visibility and faster device-level response.
- Real-time endpoint monitoring and visibility
- Behavior-based detection of suspicious activity
- Threat intelligence and forensic context
- Automated containment and endpoint response
What is XDR?
Extended Detection and Response expands beyond endpoints. It correlates telemetry from multiple security layers including endpoint, network, cloud, and email to build a more unified view of threats. XDR helps reduce alert noise, improve context, and accelerate investigation by connecting events that would otherwise remain fragmented across separate tools.
- Cross-layer visibility across the wider environment
- Threat correlation across endpoint, network, email, and cloud
- Improved root-cause identification
- Better prioritization of real risk
What is MDR?
Managed Detection and Response adds the human operational layer. It combines detection technologies with expert-led monitoring, investigation, threat hunting, escalation, and incident response. MDR is particularly important for organizations that do not have the internal staffing or security operations maturity to maintain 24/7 monitoring and response capability on their own.
- 24/7 monitoring and response support
- Human-led threat investigation and prioritization
- Proactive threat hunting
- Rapid incident response and remediation support
EDR vs XDR vs MDR — what actually matters?
The difference is not only technical. It is operational.
- EDR gives endpoint-level detection and response.
- XDR gives wider visibility and stronger threat correlation across the enterprise environment.
- MDR gives managed expertise, continuous monitoring, and active response support.
For many organizations, the practical decision is not simply which acronym sounds better, but what level of visibility, automation, and expert response is required for their environment.
Which model is right for your organization?
Choose EDR when you need stronger endpoint visibility and already have internal IT or security teams that can review alerts and respond to incidents. Choose XDR when your environment is broader and you need a unified view across endpoint, cloud, email, and network layers. Choose MDR when you need expert-led monitoring and response capability without depending entirely on internal staffing.
In many enterprise environments, the strongest answer is not one in isolation. Mature organizations often combine endpoint visibility, cross-layer correlation, and managed response to strengthen overall cyber resilience. This works especially well when paired with cybersecurity assessment and validation to identify gaps before an attacker exploits them.
Enterprise platforms we deploy
Quest Technologies Ltd approaches EDR, XDR, and MDR as solution architecture decisions supported by best-fit technologies. Depending on the client environment, business risk, and operational maturity, we help deploy and integrate enterprise-grade platforms such as CrowdStrike Falcon Insight XDR, Palo Alto Networks Cortex XDR, SentinelOne Singularity XDR, and Sophos Intercept X/XDR.
- CrowdStrike Falcon Insight XDR supports organizations that need strong threat intelligence, rapid containment, and cloud-scale visibility.
- Palo Alto Networks Cortex XDR is well suited for deeper analytics across endpoint, network, and cloud telemetry in more mature environments.
- SentinelOne Singularity XDR offers autonomous AI-driven protection and fast remediation across diverse operating systems.
- Sophos Intercept X/XDR provides strong ransomware protection and simplified management for organizations seeking practical operational efficiency.
These vendor technologies add value when they are aligned to the right operating model. The goal is not to push a badge or logo. It is to deploy a detection and response capability that matches the realities of the environment.
Detection and response maturity requires more than tooling
Security maturity is not created by software alone. It depends on visibility, escalation workflows, analyst capability, tuning discipline, incident handling processes, and the ability to act quickly when a threat develops. This is why many organizations in Kenya and East Africa are moving toward architectures that combine technology with operational response support.
The right architecture should support faster detection, stronger response, reduced alert fatigue, better investigation depth, and a more realistic ability to contain threats before they affect business operations.
How Quest Technologies Ltd helps organizations strengthen detection and response
At Quest Technologies Ltd, we help organizations assess their current visibility and response maturity, determine whether EDR, XDR, MDR, or a combination is the right fit, and deploy the appropriate controls as part of a broader security architecture. Our approach connects detection and response with identity, segmentation, monitoring, remediation, and resilience planning.
Whether the need is endpoint-focused detection, broader enterprise visibility, or managed threat response support, our goal is to help organizations build a practical, scalable, and resilient capability aligned to business reality. For organizations that also want to understand how attacks move before impact occurs, see our related insight on how cyber attacks happen in Kenya and East Africa.