The Illusion of Security
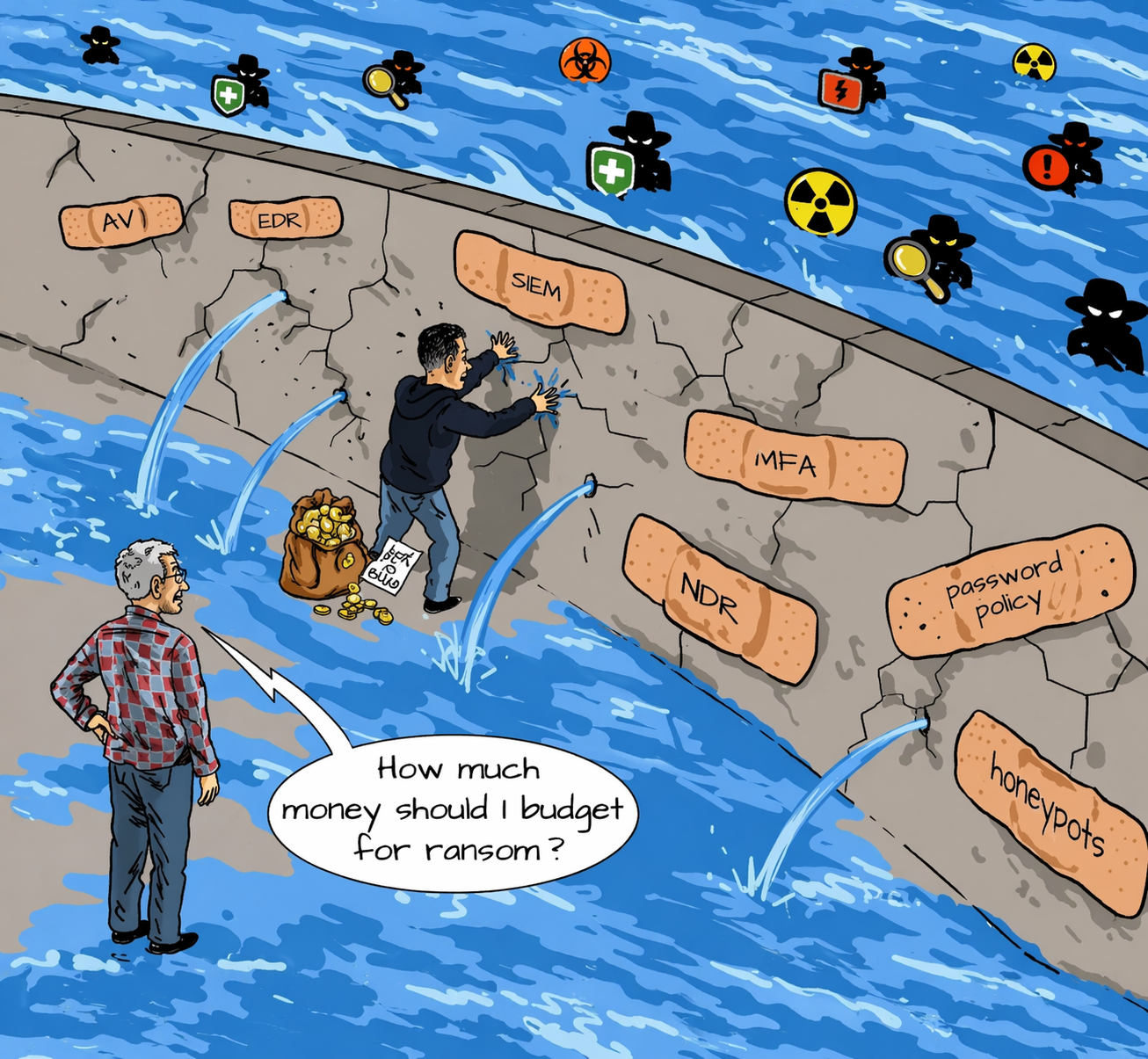
Many organizations today have invested heavily in cybersecurity tools such as antivirus, EDR, SIEM, MFA and network detection technologies.
On paper, this appears to be a strong security posture.
But in reality, attacks still get through.
The problem is not always the absence of tools. In many cases, the problem is the false confidence that tools alone are enough.
What the Wall Really Tells Us
The image above tells a powerful story.
Despite multiple security controls being in place, there are still cracks in the wall. And that is exactly where attackers enter.
This is the reality many organizations miss. Attackers do not need to break every control. They only need to find the misconfiguration, visibility gap, weak integration point, or untested assumption that no one is watching closely enough.
That is why security investments can look impressive on paper and still fail in practice.
The Core Problem: Fragmented Security
Most organizations build security in layers, but manage it in silos.
This creates fragmented environments where tools exist, but protection is not unified.
- Misconfigurations across systems
- Poor visibility between controls
- Weak integration between tools
- Limited understanding of what is actually working
- Assumptions that security is stronger than it really is
As a result, attackers do not need to defeat everything.
They simply exploit what was missed.
What Is Missing Between Tools and Real Protection
The missing layer is not another tool.
It is the discipline of continuously understanding, validating, monitoring and improving the security environment you already have.
Real protection requires organizations to know:
- Where the actual gaps are
- Which controls are effective and which are not
- What threats are emerging in the environment
- How systems, users and security controls behave together
- Where response capability is weak or delayed
Without that layer, more investment often leads to more complexity, not more protection.
Why Attackers Still Get Through
Attackers are patient.
They test weak points over time. They exploit misconfigurations, blind spots and poor coordination between controls. They move through environments that appear protected but are not being continuously validated or centrally monitored.
In many organizations, attackers understand something the defenders have not fully addressed: the tools exist, but the environment is not operating as one security system.
To understand how attackers exploit these gaps in real environments, read: How Cyber Attacks Happen in Kenya & East Africa — And How to Prevent Them.
Quest’s Position: From Tools to Real Protection
At Quest Technologies Ltd, we do not approach security as a collection of isolated products.
We begin by understanding your threat environment, assessing your current posture and validating what is already in place.
From there, we identify the real gaps, strengthen existing controls, reduce fragmentation and help organizations build security environments that are continuously monitored, continuously tested and continuously improved.
Our role is not to add noise. Our role is to help organizations move from fragmented controls to real protection.
The Continuous Security Model
Real protection requires a continuous cycle, not a one-time setup.
VAPT & Validation
Regular vulnerability assessment and penetration testing helps uncover hidden gaps, test assumptions and validate whether controls are actually working under real-world attack conditions. This is why structured validation is critical: What VAPT Means for Kenyan Enterprises, Financial Institutions and Growing Businesses.
Remediation & Hardening
Findings must lead to action. Misconfigurations, weak controls and exposure points need to be corrected, hardened and aligned to actual operational risk.
Monitoring & Detection
Organizations need continuous visibility across users, endpoints, systems and network activity to detect threats early and reduce dwell time. Continuous detection and response strengthens visibility and reduces delay: EDR vs XDR vs MDR — Which Detection & Response Solution Do You Need?.
Response & Improvement
Security must improve continuously. Monitoring, investigation, response and lessons learned should strengthen the environment over time rather than leave the same gaps open.
Enterprise Security Without Complexity
Real security is not achieved by endlessly adding more tools.
It is achieved by making the current environment work together as a unified protection model.
That means understanding how existing controls perform, aligning technologies to actual risk, eliminating fragmentation across systems, establishing centralized visibility, and maintaining continuous monitoring and improvement.
At Quest, we focus on helping organizations turn what they already have into a stronger, more coherent and more effective security environment.
The Bottom Line
The wall in the image says it all.
Breaches still happen even where multiple controls are present.
Why?
Because security is not about how many tools you own.
It is about how well they are configured, how well they are aligned, how continuously they are validated, and how effectively they are monitored.
Without that, an organization may be equipped. But it is not truly protected.